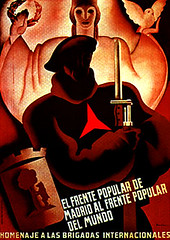
an alliance between government and commerce
In the spring of 1996, at an annual conference organized under the name "Computers, Freedom, and Privacy" (CFP), two science-fiction writers told stories about cyberspace's future. Vernor Vinge spoke about "ubiquitous law enforcement," made possible by "fine-grained distributed systems"; through computer chips linked by the Net to every part of social life, a portion dedicated to the government's use. This architecture was already being built--it was the Internet--and technologists were already describing its extensions. As this network of control became woven into every part of social life, it would be just a matter of time, Vinge siad, before the government claimed its fair share of control. Each new generation of code would increase the power of government. The future would be a world of perfect regulation, and the architecture of distributed computing--the Internet and its attachments--would make that perfection possible.
Tom Maddox followed Vinge. His vision was very similar, though the source of control, different. The government's power would not come just from chips. The real source of power, Maddox argued, was an alliance between government and commerce. Commerce, like government, fares better in a regulated world. Property is more secure, data more easily captured, and disruption is less of a risk. The future would be a pact between these two forces of social order. Code and commerce.
-from the preface of Code and other Laws of Cyberspace © 1999, Lawrence Lessig
The attribute which most singularly defines this administration is its insistence that our Government is based on unilateral and unreviewed Presidential Decree. The President directs the telecom companies to turn over this information and they obey. That’s how our Government works, as they see it. And if the telecom companies are concerned about their legal liability as a result of laws which strongly suggest that they are acting illegally if they comply with the President’s Decree, and thus request a judicial ruling first, that request, too, is denied. There is no need for a judicial ruling once the President speaks. What he orders is, by definition, legal, and nobody can say otherwise, including courts....[snip]
Magically, hordes of brilliant pro-Bush legal scholars have been able to determine instantaneously -- as in, within hours of the program's disclosure -- that the program is completely legal and constitutional (just like so many of them were able confidently to opine within hours of the disclosure of the warrantless eavesdropping program that it, too, was perfectly legal and constitutional). Having said that, there are some generally pro-Bush bloggers expressing serious skepticism over the legality and/or advisability of this program.
-Glenn Greenwald, May, 2006, from his blog. (Follow the link for the complete essay.)
A new Pentagon research office has started designing a global computer-surveillance system to give U.S. counterterrorism officials access to personal information in government and commercial databases around the world.
The Information Awareness Office, run by former national security adviser John M. Poindexter, aims to develop new technologies to sift through "ultra-large" data warehouses and networked computers in search of threatening patterns among everyday transactions, such as credit card purchases and travel reservations, according to interviews and documents....[snip]
"How are we going to find terrorists and preempt them, except by following their trail," said Poindexter, who brought the idea to the Pentagon after the Sept. 11, 2001, terrorist attacks and now is beginning to award contracts to high-technology vendors...[snip]
The office already has an emblem that features a variation of the great seal of the United States: An eye looms over a pyramid and appears to scan the world. The motto reads: Scientia Est Potentia, or "knowledge is power.
-Robert O'Harrow Jr., Tuesday, November 12, 2002,
© 2002 The Washington Post Company
House and Senate negotiators included language in the Department of Defense Appropriations Act, 2004, Pub. L. No. 108-87, § 8131, 117 Stat. 1054, 1102 (2003) signed into law by President Bush on October 1, 2003), prohibiting the further use of funds for the TIA program. Further, the Joint Explanatory Statement included in the conference committee report specifically directed that the IAO (the program manager for TIA) be terminated immediately (149 Cong. Rec. H8755—H8771 (Sept. 24, 2003). Notwithstanding the defunding of TIA and the closing of the IAO, several TIA projects continued to be funded under the classified annexes to the Defense and the Intelligence appropriation bills in 2003 and subsequently.
For example, several TIA projects were funded through the National Foreign Intelligence Program for foreign counterterrorism intelligence purposes by the National Security Agency as Advanced Research and Development Activity (ARDA) under the classified annex to the 2004 DOD Appropriations Act as contemplated in §8131 thereof. Recent reports suggest that some of this activity is now part of the Disruptive Technology Office (DTO) reporting to the Director of National Intelligence.
-Wikipedia, Information Awareness Office, article current on May 13th, 2006
1 Comments:
I highlight these quotations because they point up the troubling core of the NSA's surveillance program.
1. The NSA program was the product of cooperation between telecom corporations and the Bush administration. It's a dystopic example of the "alliance" Lessig writes about....code and commerce here being, on some level, about control.
2. Further, this cooperation of government and business, this "alliance," was (and perhaps is) ongoing and secret. There was no way for us to learn about it either as citizens through our government or as customers through the contractual relationship we have with our phone providers. Whatever we might think of NSA surveillance, we just didn't and couldn't know about it. We were cut out of the loop.
3. As Glenn Greenwald points out, presented with another instance where the Bush administration has jettissoned oversight from Congress or the Courts, it's hard to believe assurances that everything done was legal. Especially since, as he points out elsewhere in the article...the public had previously been given the clear implication that it was only domestic/international calls that had been subject to any surveillance at all.
4. Finally, not only has the Bush administration jettisoned oversight...but the "Total Information Awareness Program" had already been defunded by Congress in 2003 in part in order to avoid exactly the type of abusive reach into the private information of citizens that we now learn has been going on all along.
Post a Comment
<< Home